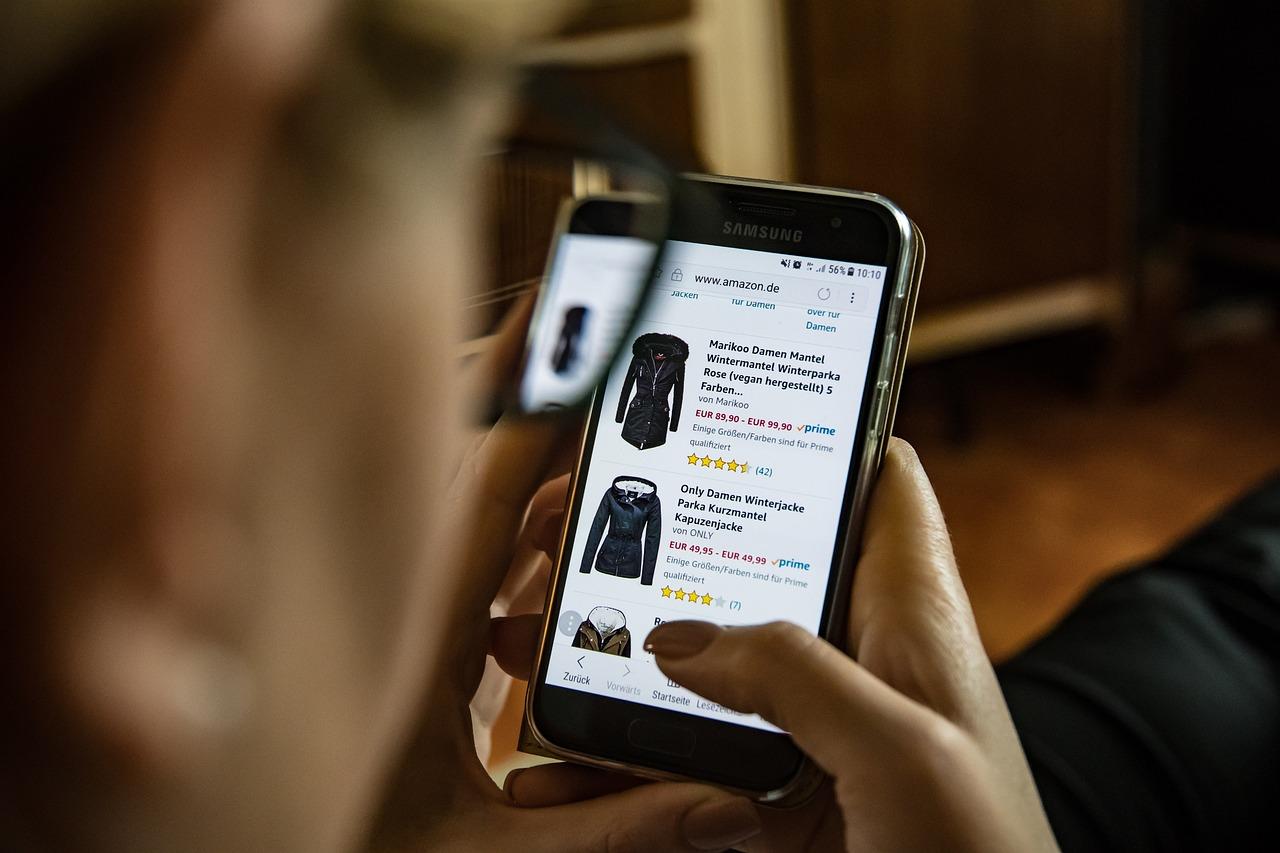
Články z rubriky „Magazín“ doprovází čtenáře v každodenním životě, pomáhá v běžném rozhodování a zjednodušuje všední záležitosti. Ať už se jedná o spolehlivé rady ohledně nákupů nebo obecné zlepšováky, příspěvky v „Magazínu“ čtenáři vždy nabízí odpovědi na jeho otázky.
Nejlepší články a návody každý den
Oblíbené příspěvky
Proč vrecenze.cz?
Články z rubriky „Magazín“ doprovází čtenáře v každodenním životě, pomáhá v běžném rozhodování a zjednodušuje všední záležitosti. Ať už se jedná o spolehlivé rady ohledně nákupů nebo obecné zlepšováky, příspěvky v „Magazínu“ čtenáři vždy nabízí odpovědi na jeho otázky.
Důvod 1
lorem ispum doromadmdf
Důvod 2
lorem ispum doromadmdf
Důvod 3
lorem ispum doromadmdf
Vše pro čerstvé rodiče
Stát se rodičem vyžaduje mnoho sil a učení se novým věcem. S webem rubrika.cz se naši čtenáři již nikdy nespletou při nákupu klasických potřeb, ale ani například s výchovnými technikami a přístupem.
Vrecenze.cz – každodenní průvodce
Internetový portál Rubrika.cz ve svých mnohých rubrikách seznamuje své čtenáře s moderním světem plným složitostí. Dnes společnost nabízí nespočet možností, ve kterých je mnohdy velmi těžké se vyznat. Proto web Rubrika.cz nabízí lidem vysvětlení a užitečné rady v mnoha oblastech.
Čtenáři na webu Rubrika.cz hledají odpovědi na otázky z oblasti rodinného života, zdraví, a nebo také podnikání, financí, či cestování. Naše příspěvky přibližují tyto a mnohé další oblasti čtenářovi, který není o dané problematice poučen. Přehledně, zřetelně a poutavě seznamujeme čtenáře webu Rubrika.cz s moderními praktikami a možnostmi v životě každý den.
Rodina je základem života
Rodina je něco, co je pro člověka základním pilířem života. Rodinu si nelze vybrat a mnohdy je těžké přijmout nebo hledat východiska v některých situacích. Přesně pro tyto komplexní situace jsou tu rady a tipy z rubriky „Rodinný život“, díky kterými lze vytěžit maximum z jakékoliv situace a zachovat rodinné vztahy.
Správná výchova dětí představuje pro mnoho rodičů tvrdý oříšek. Ve dnešním světě lze narazit na nespočet různých pohledů na výchovu těch nejmenších a mnoho rad a tipů. Díky příspěvkům na webu Rubrika.cz si v tom čtenáři mohou udělat jasno a vybrat si, co jim vyhovuje.
Finance a podnikání
Peníze jsou jedním z hlavních hybatelů společnosti. Mají neskutečný vliv na člověka a jeho okolí. Proto je potřeba být v oblasti financí znalý, aby si člověk v životě zajistil finanční stabilitu a jistotu. Rubrika „Finance“ nabízí vše, co člověk potřebuje vědět oblasti financí.
Zaměstnanec nebo zaměstnavatel? Otázka, kterou si klade veliká spousta lidí. Podnikání, ačkoliv se může zdát jako nejjednodušší způsob vydělávání, vyžaduje spoustu znalostí a správných postupů. Díky webu Rubrika.cz se již čtenáři podnikatelé nebudou muset trápit s právními náležitostmi podnikání. To a mnoho dalšího se lze dočíst v našich příspěvcích.